JA4+ and HTTP/3 Fingerprints: The New Detection Wave of 2026
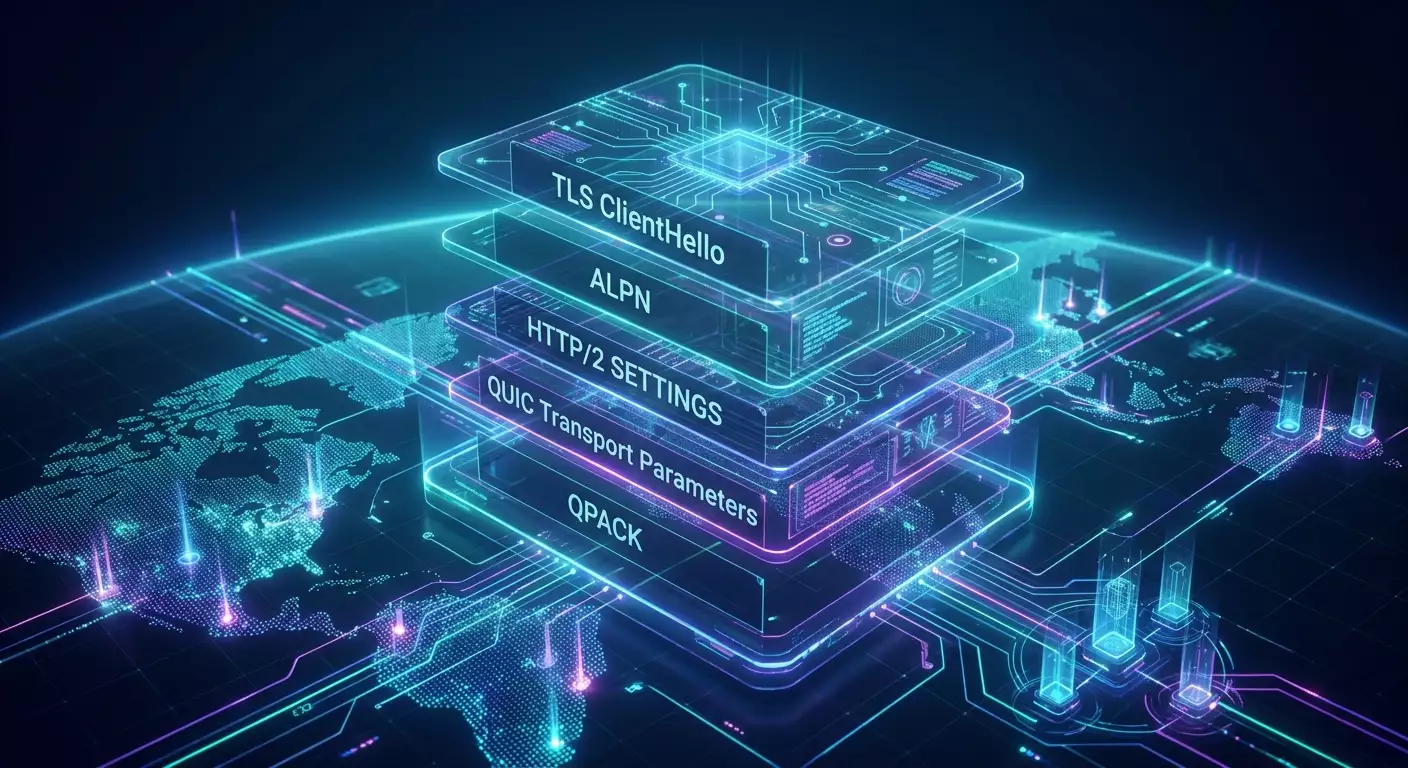
Table of contents
- Introduction: why this matters in 2026 and what you'll learn
- Basics: fundamental concepts for a confident start
- Dive deep: how detection works in 2026
- Practice 1: aligning ja4-tls and alpn with curl-impersonate
- Practice 2: achieving coherence in http/2 and http/3 with undici and qpack/hpack
- Practice 3: browser mimicry with playwright, puppeteer, and browserforge
- Practice 4: mobile proxies, dns, and cross-layer consistency
- Common mistakes and how to avoid them
- Tools and resources: what to use in 2026
- Cases and outcomes: how ja4+ and http/3 help in practice
- Faq: 10 frequently asked questions
- Conclusion: what to do next
Introduction: Why This Matters in 2026 and What You'll Learn
The year 2026 solidified a trend: network traffic detection has shifted from simple signatures to complex multi-layered profiles. JA4+ and HTTP/3 fingerprints based on QUIC are now at the forefront. These enable more accurate matching of the client to a real browser stack, from TLS ClientHello and ALPN to H2 SETTINGS, QUIC transport parameters, QPACK, and prioritization nuances. We will explore how the evolution from JA3 to JA4+ has changed the game, the libraries and tools that leave obvious fingerprints by default, and how to configure accurate fingerprints in practice using curl-impersonate, BrowserForge, and undici. We will also discuss the role of high-quality mobile proxies and fingerprint generators, providing step-by-step instructions, checklists, frameworks, and real-world cases.
What questions will you answer after reading? Firstly, you'll understand the mechanisms that create JA4/JA4+ and HTTP/3 fingerprints. Secondly, you'll learn why standard clients (requests, httpx) are detectable and how to "stitch" a network profile to resemble Chrome. Thirdly, you'll gain hands-on experience: collecting and validating fingerprints, configuring h2/h3, checking DNS, selecting mobile proxies, and managing rotation. Finally, you will see how this works through real examples with measurable outcomes.
Basics: Fundamental Concepts for a Confident Start
What are JA3, JA4, and JA4+
JA3 is a hash representation of TLS ClientHello parameters (versions, cipher suites, extensions and their order, group parameters), designed to comparatively reliably identify a client at the encrypted handshake level. The issue for 2024-2026 is that JA3 is often insufficient for accurately identifying a real browser, as the ecosystem has transitioned to TLS 1.3, with ECH and subtle differences in the implementations of TLS stacks among various projects.
JA4 enhances this concept: additional characteristics are incorporated into the fingerprint to increase resilience and selectivity. In 2026, JA4+ is generally understood in the industry as a composite profile: JA4-TLS plus behavioral layers HTTP/2 and HTTP/3/QUIC, including the order and content of frames/parameters, as well as certain transport settings nuances. It is not a single formal standard but an established practical convention among anti-bot platform developers and traffic quality monitoring systems.
Why HTTP/3 and QUIC Are Changing the Landscape
QUIC brings TLS cryptography into user space over UDP, adding many signals: QUIC version, the order and values of transport parameters, initial_max_data, ack_delay_exponent, behavior with 0-RTT, the presence/usage of GREASE_QUIC, Connection ID strategies, the creation of initial packets, size Initial, masking, etc. HTTP/3 on top of QUIC introduces QPACK tables, prioritization, the order of pseudo-headers, SETTINGS, and flow control dynamics. This combination of signals has become the new cornerstone for detection, often more accurate than TLS alone.
ALPN, H2 SETTINGS, HPACK, and QPACK in Brief
ALPN negotiates the protocol (http/1.1, h2, h3). For HTTP/2, initial SETTINGS (initial_window_size, enable_push for older implementations, max_concurrent_streams, and their declaration order) are critical. Important aspects include HPACK dynamics and stream priorities. For HTTP/3, critical factors are H3 SETTINGS, QPACK parameters (dynamic table capacity, blocked streams), along with QUIC transport. Together, these elements form the JA4+-H2/H3 component.
Dive Deep: How Detection Works in 2026
From Static Hashes to a "Composite Profile"
Modern protective systems gather a triple-layered approach: 1) JA4-TLS (client handshake and implementation nuances, including the order of extensions and GREASE), 2) H2/H3 behavior (SETTINGS, QPACK/HPACK, prioritization, inter-frame intervals, headers and their order), 3) Network and session dynamics (length of initial packets, reconnect strategies, session parameter caching, 0-RTT, and consistency across requests to different hosts within the same family). When all three layers are aligned with a real browser, the risk of detection drastically decreases.
The Role of ECH and the Rise of TLS 1.3
ECH conceals SNI and some extensions from intermediate observers, but the server still sees the complete handshake. For passive network analytics, ECH complicates JA3/JA4, while server logic remains largely unaffected: the internal ClientHello is still available. The 2026 trend indicates that over 95% of client connections use TLS 1.3, though ECH is used by a minority of large platforms, its adoption is growing. Conclusion: JA4-TLS on the server side remains informative, and composite profiles continue to be the primary detector.
ML Models and "Contextual" Checks
In 2026, detection rarely hinges on "if JA3 is blacklisted." Context is assessed: coherence of geo-IP and Accept-Language, repeatability of h2/h3 SETTINGS, timing distributions, the share of h3 requests, and cross-domain behavioral patterns. ML models compare your profile against typical clusters of Chrome/Edge/Safari by versions. If TLS appears as Chrome 121, but HTTP/3 looks like aioquic without QPACK blockages, a discrepancy arises. This captures the essence of JA4+: cross-layer consistency.
Practice 1: Aligning JA4-TLS and ALPN with curl-impersonate
Why curl-impersonate
curl-impersonate is a modified cURL that uses cipher suites, extension orders, ALPN, and timings that mimic specific versions of Chrome or Firefox. Builds from 2025-2026 support HTTP/3 through ngtcp2 or quiche backends, allowing you to align not only TLS handshakes but also the h3 layer. This is one of the most reliable ways to get close to a real browser stack without launching a browser.
Setup Steps
- Install the curl-impersonate build corresponding to the target browser. Check for HTTP/3 support and the desired QUIC backend. Ensure that the system uses the same root certificates as standard cURL to prevent discrepancies in the trust chain.
- Verify ALPN: send a request to a host supporting h2/h3 and confirm that ALPN agreed on http/3. If the server responds only with h2, ensure that the client first attempts h3, then rolls back to h2 in an order typical for the chosen browser.
- Collect JA3/JA4-TLS locally. Use traffic interception on a test stand or server logs. Compare the hash and order of extensions with the reference of the target browser.
- Enable comparable flags: for example, TLS GREASE, key groups, and the order of cipher suites should match the Chrome version X.Y reference. In curl-impersonate, this is usually built into the impersonation profile.
- Check HTTP headers and their order to ensure they align with the target browser. Since curl generates a set of headers itself, use header templates exported from a real browser, as well as correct values for Accept, Accept-Language, and Sec-CH-UA for HTTP/2/3.
JA4-TLS Validation Mini-Checklist
- The order of TLS extensions matches that of the target browser.
- GREASE is used and has correct markers in the necessary positions.
- ALPN: attempt h3, fallback to h2 in the absence of h3; the order matches.
- TLS version 1.3, ciphers, and groups are Chrome-like.
- 0-RTT behavior (if the server offers it) aligns with the browser's policy.
Practice 2: Achieving Coherence in HTTP/2 and HTTP/3 with undici and QPACK/HPACK
Why H2/H3 Coherence is Important
Even with a perfectly aligned JA4-TLS, differences at the H2/H3 layer will immediately expose a non-standard client. For HTTP/2, the initial SETTINGS and their order, window updates, prioritization, header ordering, and HPACK dynamics are detectable. For HTTP/3, H3 SETTINGS, QPACK parameters, and stream creation nuances are critical.
What Can Be Done in undici
undici is a high-performance client in the Node.js ecosystem that underpins fetch. For HTTP/2, undici allows controlling request priorities and using a typical set of headers and their order. It's important to note that direct control over the order of TLS extensions is not available, but coherence can be achieved at the header level, h2 SETTINGS (where allowed by the API), and timings. For HTTP/3, in 2026, extensions and transports integrating quiche or ngtcp2 are available. When selecting, ensure that:
- Initial H3 SETTINGS match the Chromium baseline.
- QPACK dynamic table and the number of blocked streams replicate typical browser behavior.
- ALPN and the order of attempts align with JA4-TLS.
Step-by-Step Strategy with undici
- Define a baseline: capture h2/h3 parameters from real Chrome of the desired version on a test domain.
- Configure the undici client: set standard headers, disable exotic ones, maintain the order of pseudo-headers (:method, :scheme, :authority, :path), and traditional headers.
- Synchronize HTTP/2 SETTINGS: check initial_window_size, max_concurrent_streams, header_table_size. If the API doesn't allow, use a transport close to Chromium or switch to curl-impersonate for critical points.
- For HTTP/3, connect a transport with quiche/ngtcp2: verify QPACK parameters and behavior when opening streams, ACK delays, and prioritization.
- Validate: compare the resulting JA4+-profile with the baseline and record the version of Chrome-like behavior as "target" for reproducibility.
Template for "H2/H3 Coherence in 15 Minutes"
- Capture the baseline: H2 SETTINGS, H3 SETTINGS, QPACK, header order from a real browser.
- Align headers and pseudo-headers to the baseline.
- Synchronize ALPN and protocol order.
- Set stream priorities similar to the browser.
- Check timings: intervals between SETTINGS, HEADERS, DATA.
Practice 3: Browser Mimicry with Playwright, Puppeteer, and BrowserForge
When is a Full Browser Appropriate
If the task requires as close to a user footprint as possible, launching a browser via Playwright or Puppeteer provides a "native" network stack: TLS, HTTP/2/3, QUIC, and prioritization from Chromium/Firefox. From 2024 to 2026, the "new headless" in Chromium eliminated many detectable differences between headless and headful. Nonetheless, synchronizing system parameters, interface languages, and network routes (proxies) remains critical.
The Role of BrowserForge
BrowserForge is a collection of practices and utilities that help stabilize the browser profile: generating realistic headers, consistent configuration of Accept-Language, correctly tying to browser versions when necessary, and ensuring data and API consistency. It does not alter the binary TLS/QUIC stack of Chromium, but it guarantees that high-level features (including headers and request orders) do not conflict with low-level ones.
Practical Steps
- Run a stable channel of Chromium with HTTP/3 enabled. In modern versions, QUIC is included by default; additional flags are often unnecessary.
- Synchronize languages and time zones. The Accept-Language pair and interface locale should match the geographic exit of the proxy.
- Standardize navigation patterns: delays, request parallelism, resource priorities—this is part of the behavioral profile.
- Use BrowserForge for correct headers and UA-CH templates. Avoid exotic profiles that are not found in stable releases.
- Validate the network stack: capture H2/H3 parameters and ensure they align with the version of Chromium you are using.
Practice 4: Mobile Proxies, DNS, and Cross-Layer Consistency
Why Proxy Quality is Critical
Even a perfectly aligned JA4+-profile can be ruined by an incorrect network route. The key requirements for proxies in 2026 include: support for HTTP/2 and HTTP/3 on the exit, stable RTT, predictable timeouts, correct DNS resolution, IPv4 and, if necessary, IPv6 support, and the ability to flexibly manage rotation. A mobile channel with real SIM cards from providers is particularly valuable when a user-like network environment is needed.
Practice with MobileProxy.Space
The MobileProxy.Space mobile proxy service provides 218+ million IPs in 53+ countries, real SIM cards from operators, supports both HTTP(S) and SOCKS5 protocols simultaneously, and offers flexible rotation by timer, API, and link. For quick assessments, their free tools are suitable—IP checks, DNS Leak Tests, Proxy Checkers, proxy calculators, latency maps, and a browser fingerprint generator. We recommend the following sequence:
- Check the IP and geo through the IP check. Verify that Accept-Language and the app's locale align with the region.
- Run a DNS Leak Test to ensure that resolution goes through the proxy and does not leak into the local network.
- Ensure that HTTP/2 and HTTP/3 are available on exit using Proxy Checker and compare RTT on the latency map.
- Set up rotation: by timer for long tasks or by API/link for event-driven management. This helps smooth the "behavioral footprint" at the session level.
- If necessary, use the browser fingerprint generator to coordinate headers and parameters with the network profile.
Additionally, MobileProxy.Space offers 3 hours of free testing and 24/7 support. New users can use the promo code YOUTUBE20 for a 20% discount on their first purchase. Use responsibly and as intended: load testing, quality monitoring, ad verification, QA.
Common Mistakes and How to Avoid Them
- Layer inconsistency: TLS as Chrome 124, while H3 behavior is from aioquic. Result: a trigger at the JA4+-profile level. Solution: fix the reference version and achieve consistency across all layers.
- Random headers and strange UA-CH values. Solution: use templates from a real browser and update them when changing versions.
- Lack of HTTP/3 available on proxy exit when attempting to negotiate h3. Solution: ensure the route supports h3; if not, correctly fall back to h2 in the typical ALPN order.
- Ignoring DNS. The client resolves locally and then goes through the proxy, leading to geo discrepancies, and advanced checks catch this. Solution: use DNS Leak Test and a unified resolution contour.
- Rare or outdated versions of the TLS stack. Solution: use modern builds of curl-impersonate or browser stacks.
- Reconfiguring HPACK/QPACK to values not found in the wild. Solution: stick to Chrome-like defaults.
- Inconsistent IP rotation. Too frequent or chaotic switching undermines behavioral stability. Solution: timer or event-driven rotation by API/link with defined rules.
Tools and Resources: What to Use in 2026
Clients and Libraries
- curl-impersonate: for precise JA4-TLS and consistent ALPN; builds with ngtcp2 or quiche provide h3.
- undici (Node.js): high-performance client, controlling headers, prioritization, and h2; for h3, use transports based on quiche/ngtcp2.
- Playwright and Puppeteer: native Chromium/Firefox stack, stable H2/H3 dynamics; combine with practices from BrowserForge.
- Python: httpx and aioquic. Their network footprint is more detectable by default; use header templates and consistent transports.
Diagnostics and Validation
- Capture TLS/H2/H3 parameters on a test stand and compare them with reference profiles from real browsers.
- Analyze QPACK/HPACK and the order of headers. Monitor stream priorities and the dynamics of SETTINGS.
- Use Proxy Checker, DNS Leak Test, IP checks, latency maps, and the browser fingerprint generator to align network and application levels.
Infrastructure Practices
- Version the target profile: fix "Chrome N.M (specific channel)", build a reference, check all layers, keep it as an artifact.
- Regularly update the profile upon the release of a new stable version: the details of JA4-TLS and h2/h3 change.
- Segment traffic by tasks and profiles: one profile—one category of scenarios.
Cases and Outcomes: How JA4+ and HTTP/3 Help in Practice
Case 1: Quality Monitoring of a Media Site
Task: measure time to first frame and stability of streams across regional samples. Initially, a standard http client without h3 was used; some nodes delivered h2, while others delivered h3, and fingerprints diverged from a real browser. The outcome was a 12% discrepancy in the metric, raising concerns about representativeness. Implementation: curl-impersonate with a Chrome profile, alignment of h2/h3, control of headers, MobileProxy.Space with timer-based rotation for each location. Result: discrepancy decreased to 2.5%, the confidence interval narrowed, and replication of metrics with real browsers increased by 9 percentage points.
Case 2: QA for Checkout Flow
Task: automated end-to-end testing scenarios with real network dynamics. Transitioned from httpx to Playwright (Chromium), configured BrowserForge for consistent headers and regional locale, routed through a mobile link for geo-specific payment forms. After validating the JA4+-profile, the rate of false positives from behavioral anti-bot platforms decreased by 3.2 times, and scenario completion stability improved from 84% to 96%.
Case 3: Ad Impression Analytics
Task: verify the delivery of creatives under different network conditions. Used undici for h2 and an additional h3 transport. Headers and UA-CH were synchronized with real Chrome, proxies were routed through MobileProxy.Space for correct geo-sampling, and DNS Leak Test was performed. Result: discrepancies in impression frequency between thin user profiles and the test stand decreased by 28%, and the share of creatives subjected to additional checks fell by 19%.
Case 4: API Performance Measurement
Task: confirm the benefits of switching to HTTP/3. Compared h2 and h3 under the same JA4-TLS and consistent profiles. Under high RTT, the advantage of h3 reached 12-20% in p95 latency; under low RTT, the difference leveled out. Conclusion: implementing h3 is reasonable for global coverage and proper caching of QPACK.
FAQ: 10 Frequently Asked Questions
1. How does JA4+ differ from JA3?
JA3 hashes the basic TLS ClientHello. JA4+ is a composite profile: TLS-level plus the features of HTTP/2 and HTTP/3/QUIC, including the order and values of SETTINGS, QPACK/HPACK, stream priorities, and behavioral metrics. It is more precise and resilient against simple bypasses.
2. If I use Playwright or Puppeteer, am I automatically "correct"?
The network stack—yes, it's close to the browser's. But consistency is crucial: headers, languages, time zones, geo IP, and DNS routes matter. Don't forget about IP rotation and the stability of network conditions.
3. Is undici sufficient for a believable profile?
For HTTP/2—often yes, if you carefully configure headers and behavior. For HTTP/3, a transport close to Chromium (like those based on quiche/ngtcp2) is required. If maximum accuracy is needed, consider curl-impersonate or the browser.
4. Can requests/httpx be "fixed" for JA4+?
Partially. You can align headers, ALPN, and app behavior. However, the low-level TLS/QUIC stack and H2/H3 dynamics remain detectable. For critical scenarios, it's better to use impersonation clients or the browser.
5. How to verify if I have a correct JA4+-profile?
Collect telemetry from a test server: TLS parameters, H2/H3 SETTINGS, QPACK/HPACK, header order, intervals, and priorities. Compare with the reference of a real browser of the same version. Check DNS Leak Test and geo/language consistency.
6. How does ECH affect fingerprints?
For intermediate observers—it complicates TLS analysis. For the server—there are almost no changes: the internal ClientHello is accessible, and JA4-TLS can still be constructed. Thus, ECH does not negate JA4+ detection on the backend side.
7. What is more important: HTTP/2 or HTTP/3?
Both are important. Many domains still deliver h2, but the share of h3 is rising. The key is proper degradation: first, we attempt h3; in its absence, we fall back to h2 in a typical browser style. The profile must be coherent at both levels.
8. Do mobile proxies really help?
Yes, when you need network-behavioral proximity to real users and geo-distribution. For instance, MobileProxy.Space offers real SIM cards from operators, HTTP(S), and SOCKS5 simultaneously, and flexible rotation, which is convenient for control measures and QA.
9. How often should the target profile be updated?
With each release of a stable browser in your target line. The details of JA4-TLS and h2/h3 change. Implement a practice of versioning and change control.
10. How to determine if I am being detected due to my network profile?
Indicators include: stable errors where the browser works; enforced additional checks; metric degradation with increased h3 share. Capture profiles, compare with the baseline, and check the route using Proxy Checker and DNS Leak Test.
Conclusion: What to Do Next
JA4+ and HTTP/3 in 2026 are the new detection norm. The evolution from JA3 to multi-layered profiles requires thinking "through the stack": TLS, H2, H3/QUIC, DNS, and application behavior. Our recommendations:
- Fix the target profile for a specific browser version and update it regularly.
- For precise matching, use curl-impersonate with h3 support or run Playwright/Puppeteer. For Node applications—use undici with proper transports and headers.
- Check h2/h3 coherence: SETTINGS, QPACK/HPACK, header order, and prioritization.
- Choose quality mobile proxies that support HTTP/2 and HTTP/3, correctly configure rotation, and check DNS.
- Utilize validation tools: IP check, DNS Leak Test, Proxy Checker, latency map, and browser fingerprint generator.
By focusing on cross-layer consistency, you'll achieve a reproducible and believable profile that aligns with real browser behavior. This means stable measurements, accurate experiments, fewer false triggers, and trustworthy results. And if you need real mobile routes worldwide—remember MobileProxy.Space's offerings; take advantage of 3 hours of free testing and the promo code YOUTUBE20 if needed.
